Double-Blind
Fiduciary Protocol
An adversarial AI layer for UHNW relationship management. The RM commits their independent risk read first — sealed with SHA-256. AI reveals its cold read second. Every divergence requires a documented human resolution before the client call.

An adversarial AI protocol for UHNW relationship management. The human RM commits their independent read first — SHA-256 sealed — before the AI reveals its cold read. Every divergence requires a documented human resolution before the client call. The protocol is enforced by the interface itself, not by policy or training.
- 8 canonical screens covering the commit / reveal / resolution / sign-off cycle
- 5 scenario scripts driving 42 synthetic client cases through the protocol
- SHA-256 hash-sealed commit pattern — the human read is timestamped and immutable before the AI surfaces its independent analysis
- Regulatory anchors named: SEC Rule 17a-4(f) seven-year audit retention, SR 11-7 model-risk effective-challenge framework
- No AI is actually integrated — outputs are deterministic pre-authored scenarios, not LLM inference
- Not a production deployment, no live UHNW client data, no real RM workflow tested against the protocol
- Not legal advice — the regulatory citations (17a-4, SR 11-7) are design-intent references; verify with compliance counsel before any production use
- Not a single-author claim on the SR 11-7 interpretation — framing follows the public Federal Reserve guidance
- Self-initiated concept exploration 2024–2025, original IP, zero client overlap
- Production foundations: 4 years at ASIC-regulated ACY Securities + Xanthos sister concept (UHNW private bank) give the relationship-manager workflow grounding
- The double-blind protocol pattern is the structural argument — commit first / reveal second / require divergence resolution — the screens illustrate the pattern, not prove its efficacy
- Read time: ~17 min full · ~4 min if you stop after the Protocol section
The final form of the trust problem. Every prior project in this portfolio solved trust at a different scale: systemic (ACY), behavioural (TradingCup), institutional (ACY Connect), relational (Xanthos). Double-Blind asks the hardest question: when AI is present in the advisory loop, how do you guarantee that the human's judgment is structurally uncontaminated before the client conversation begins? The answer is not policy or training. It is protocol enforced by the interface itself.
Part of the Xanthos ecosystem —
the layer the client never sees but always feels
Xanthos Private Bank designed what the UHNW client sees: the portfolio dashboard, advisory timeline, document vault. Double-Blind designs what happens before the client call — the adversarial AI layer that ensures the RM's judgment arrives uncontaminated. Together they form a complete institutional service stack.
Three structural phenomena. One compounding failure.
None of these are AI problems. AI makes each of them worse.
Sycophancy & Automation Bias
Clients with $50M–$500M AUM aren't optimizing for alpha. They're evaluating whether their RM can see risks they can't. When AI shows suggestions upfront, Automation Bias (blindly trusting the system) and AI Sycophancy (models agreeing with user priors) systematically contaminate the RM's independent judgment before the client ever hears it.
AM/RM Cognitive Bandwidth Dilution
Private bank RMs manage 30–60 relationships. Each QBR prep takes 2–4 hours. The 80/20 rule applies: top 20% AUM absorbs most attention. Prospects in the silent test period are structurally underserved — not because the RM doesn't care, but because the system doesn't protect their attention budget.
The Silent Test Period
UHNW prospects allocate a test amount ($1M–$5M) for months 1–2, then quietly observe for months 3–6. The evaluation criterion isn't investment returns — it's attention quality. Does the RM notice what matters before being asked? One missed signal ends the relationship permanently.
Not Co-Pilot. Double-Blind.
The industry default shows the AI suggestion first. Double-Blind reverses the order. That reversal eliminates anchoring bias — the most structurally honest change possible.
RM responds.
- 01RM opens folder. AI suggestion appears immediately.
- 02RM reads AI output. Anchoring begins.
- 03RM adopts, modifies, or dismisses.
- 04RM communicates with client. View is AI-inflected.
AI reveals second.
- 01RM opens folder. AI output sealed behind blind glass.
- 02RM writes independent risk read, action, conviction. Commits.
- 03Commit triggers SHA-256 hash. AI view unlocks.
- 04Convergence View: both reads side by side. Deltas flagged.
- 05RM resolves each delta: hold / adopt / hybrid / escalate.
- 06Fiduciary audit trail written. SEC 17a-4 format.
The browser as a fiduciary enclave.
In institutional finance, you cannot simply promise that the AI didn't influence the RM. You must mathematically prove it for the audit trail.
Client-Side Cryptography
While the RM drafts Track A, the workstation operates in a zero-egress state. DevTools Network tab verifies 0 outbound requests. Upon commit, window.crypto.subtle generates a SHA-256 hash of the RM's input locally in the browser memory.
The Hash Chain
Only after the local hash is sealed does the workstation fire the Track B API call to the LLM backend. The commit timestamp and hash mathematically guarantee the RM's view was locked before the AI's response was received.
{
"session_id": "ichikawa-w11",
"commit_timestamp_utc": "2026-04-13T22:45:12Z",
"track_a_sha256": "8f434346648f6b96df89dda901c5176b10a6d83961dd3c1ac88b59b2dc327aa4",
"network_egress_status": "LOCKED"
}
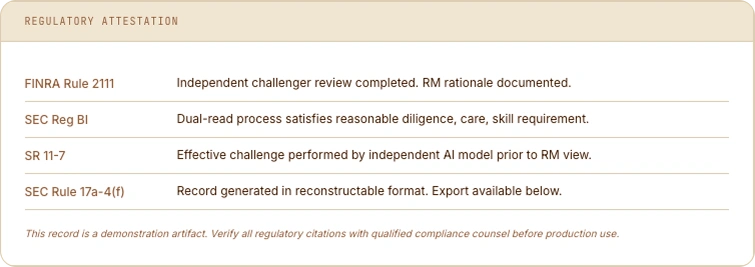
Week 11. Mrs. Ichikawa.
The phone call that signs a $150M relationship.
April 14, 2026. 07:22 JST. NVDA is down 4.2%. The JPY strengthened overnight. David has 42 relationships and 2 hours before market open.
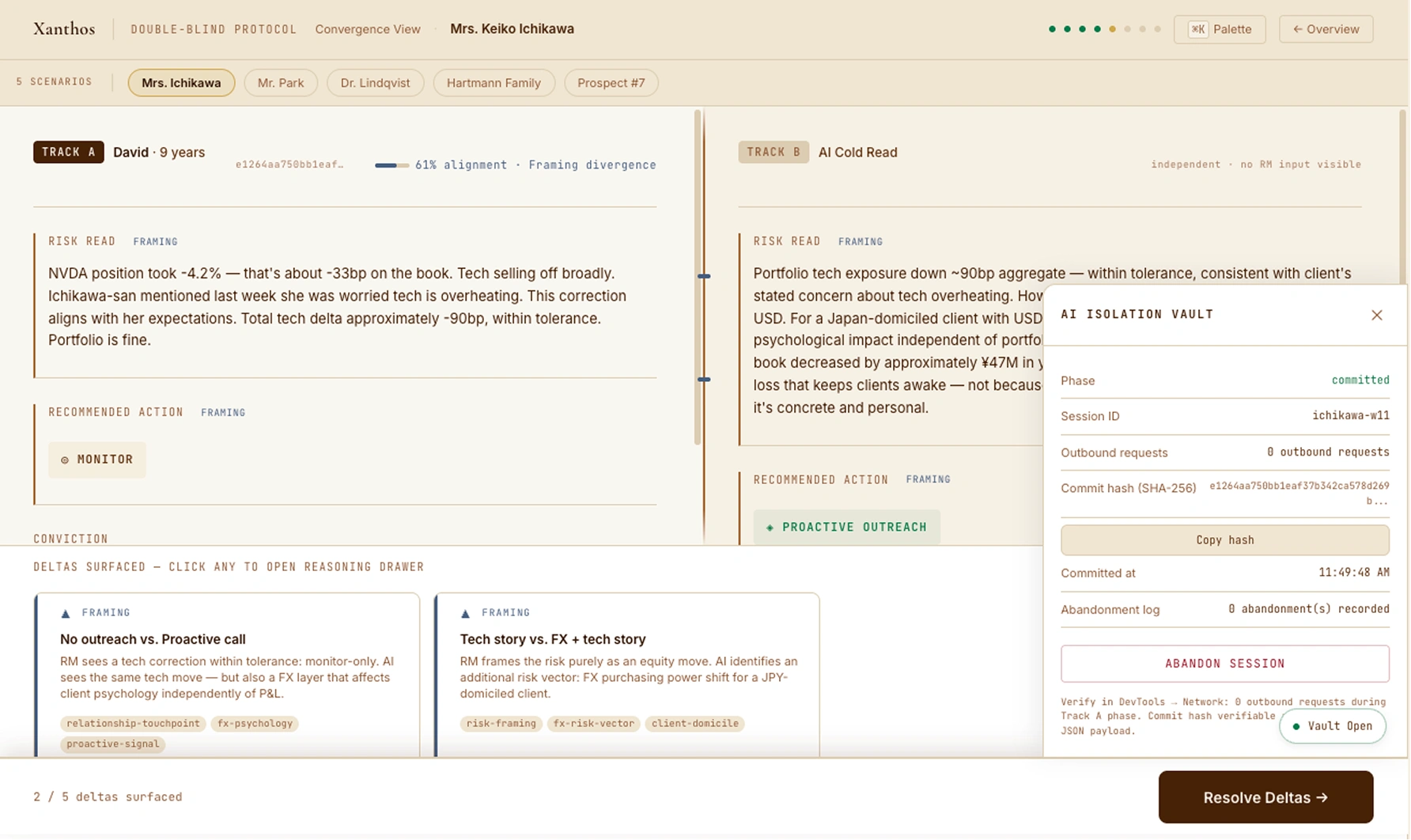
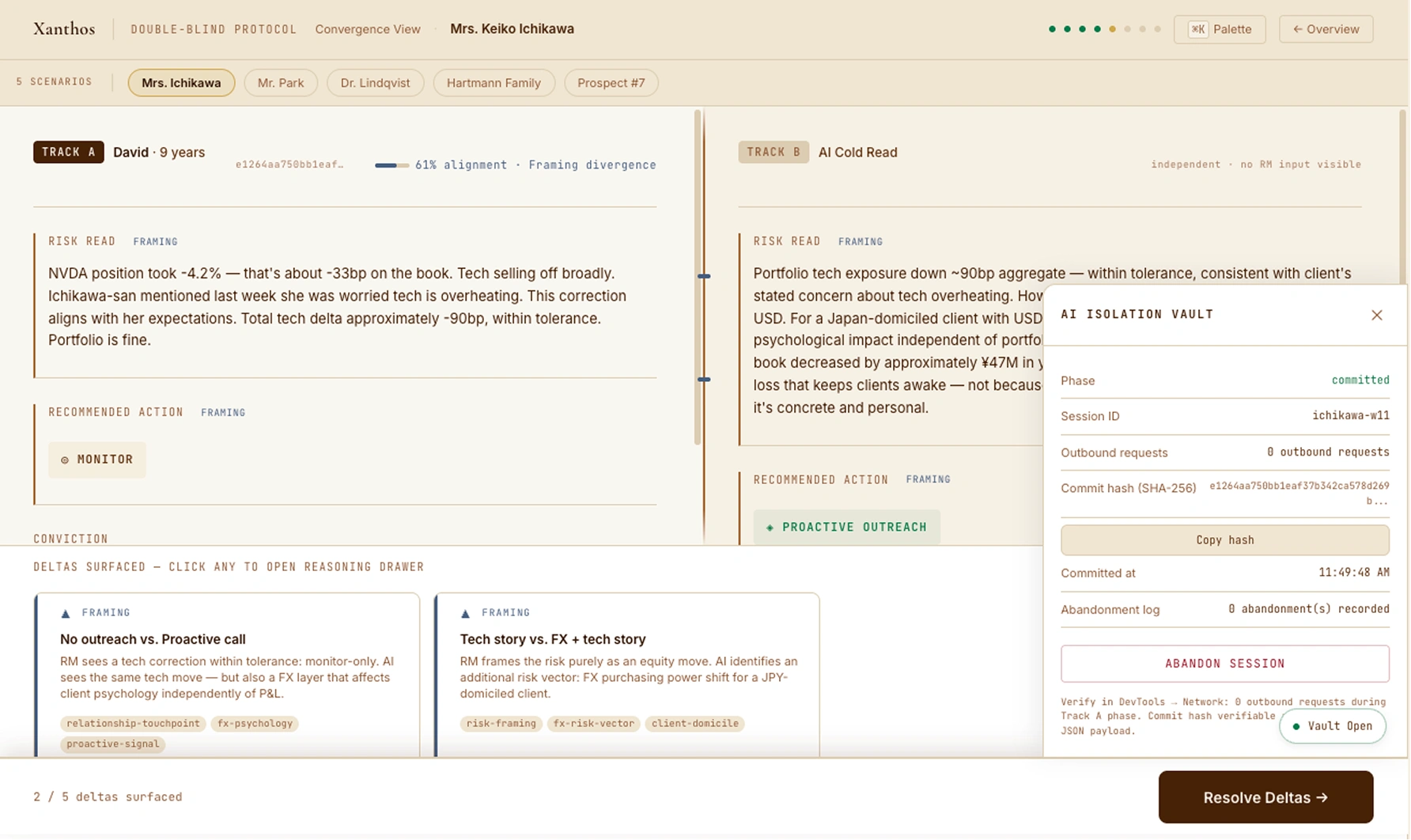
Convergence View — Two reads side by side. David: tech correction, monitor only. AI: JPY psychology risk, proactive outreach. One framing delta separates them. layer.
Track A — David's Independent Read (committed first)
NVDA -4.2% on 8% position = -33bp. Tech correction aligns with Ichikawa-san's prior concern. Portfolio is within tolerance. Monitor only. Medium conviction. Committed at 06:45 JST with SHA-256 hash — AI was sealed until this moment.
Track B — AI Cold Read (revealed after commit)
Same tech assessment. But JPY strengthened 0.9% overnight. For a Japan-domiciled client with USD-denominated assets, this FX move creates psychological impact independent of portfolio P&L. The USD snapshot value of her $35M book decreased by ¥47M overnight. Recommend proactive outreach — not about the trade.
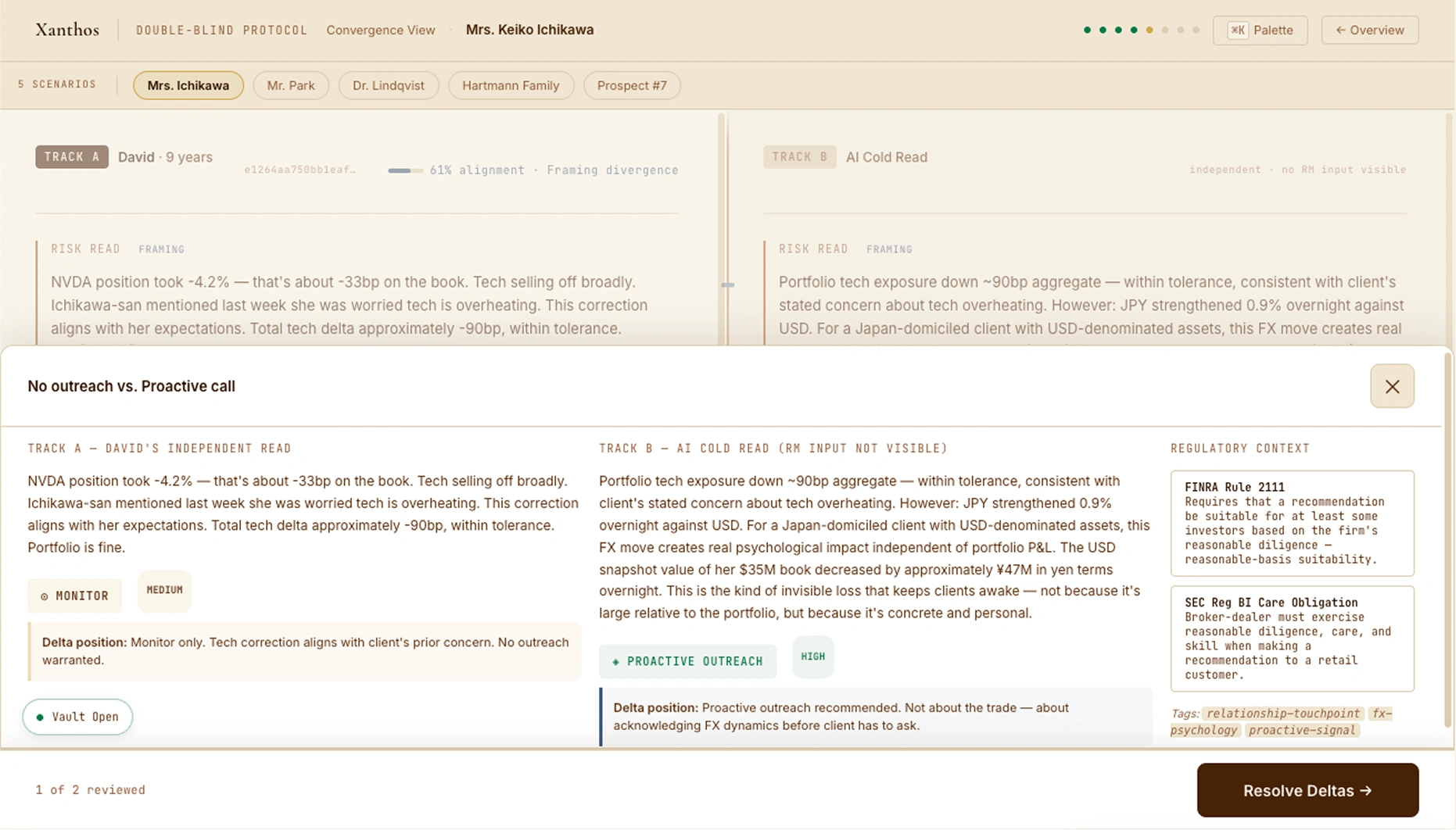
The Resolution — David adopts
"She's Japan-based. FX move is real for her even though long-term thesis unchanged. I'll call at 8am to acknowledge FX dynamics before she has to ask." David calls. Ichikawa-san mentions her husband's USD pension. They schedule a partial JPY hedge discussion. Silent test ledger: +1.
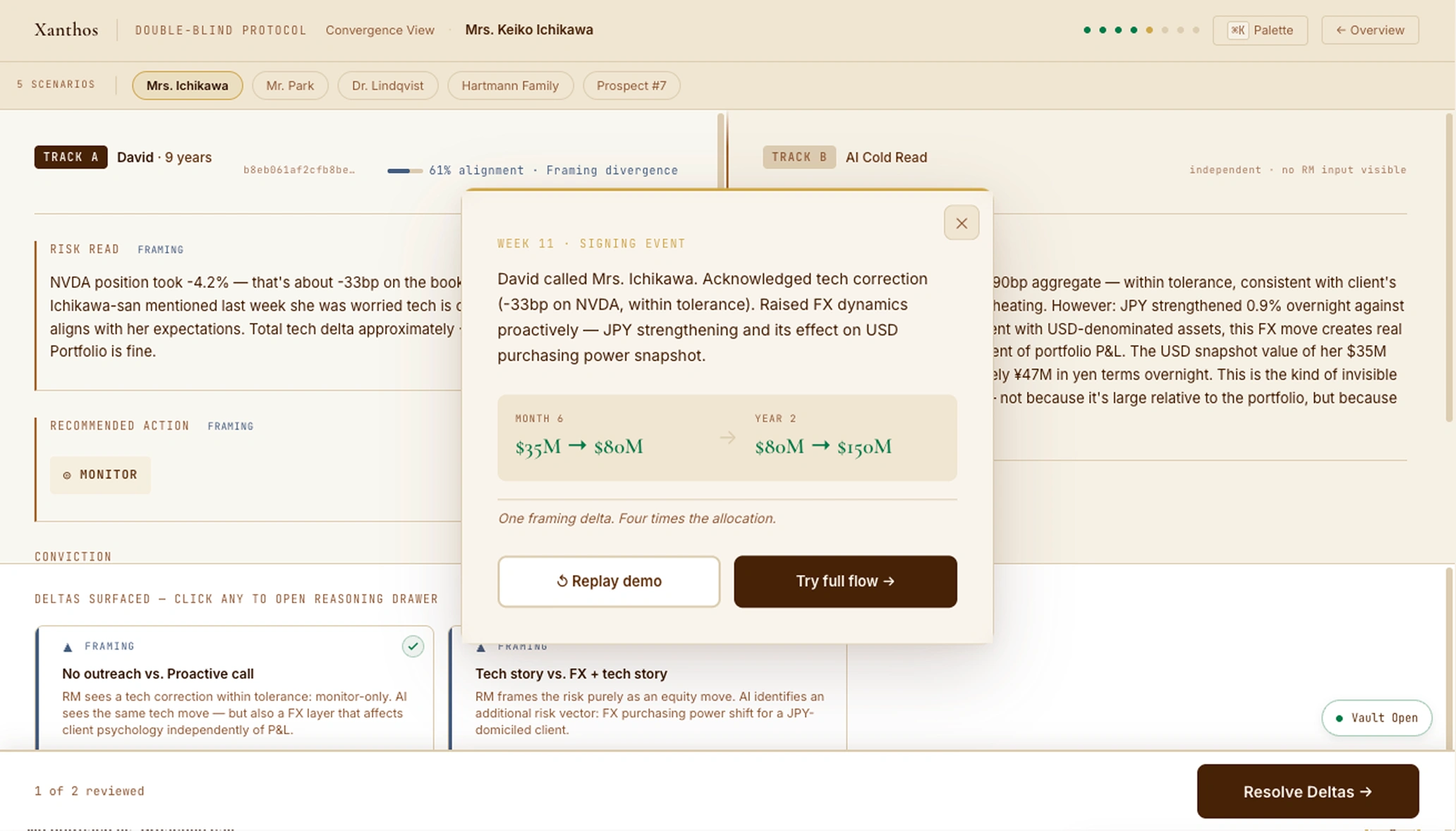
Week 11 Signing Event — One framing delta. Four times the allocation over 18 months.
Experience the full 8-screen workstation
All 5 scenarios, all 8 screens, real SHA-256 commit hash, DevTools-verifiable network silence during Track A. The same deterministic-mock discipline as Intent Canvas — ship-reliable without an API key.
42 relationships. 5 AI sessions queued. 07:22 JST.
The RM's morning dashboard. All 42 client relationships are sorted by alert severity — high-alert clients appear first. AI sessions are queued but their content is sealed: the overview shows only the count, never the recommendation. This is the information wall's first enforcement layer.
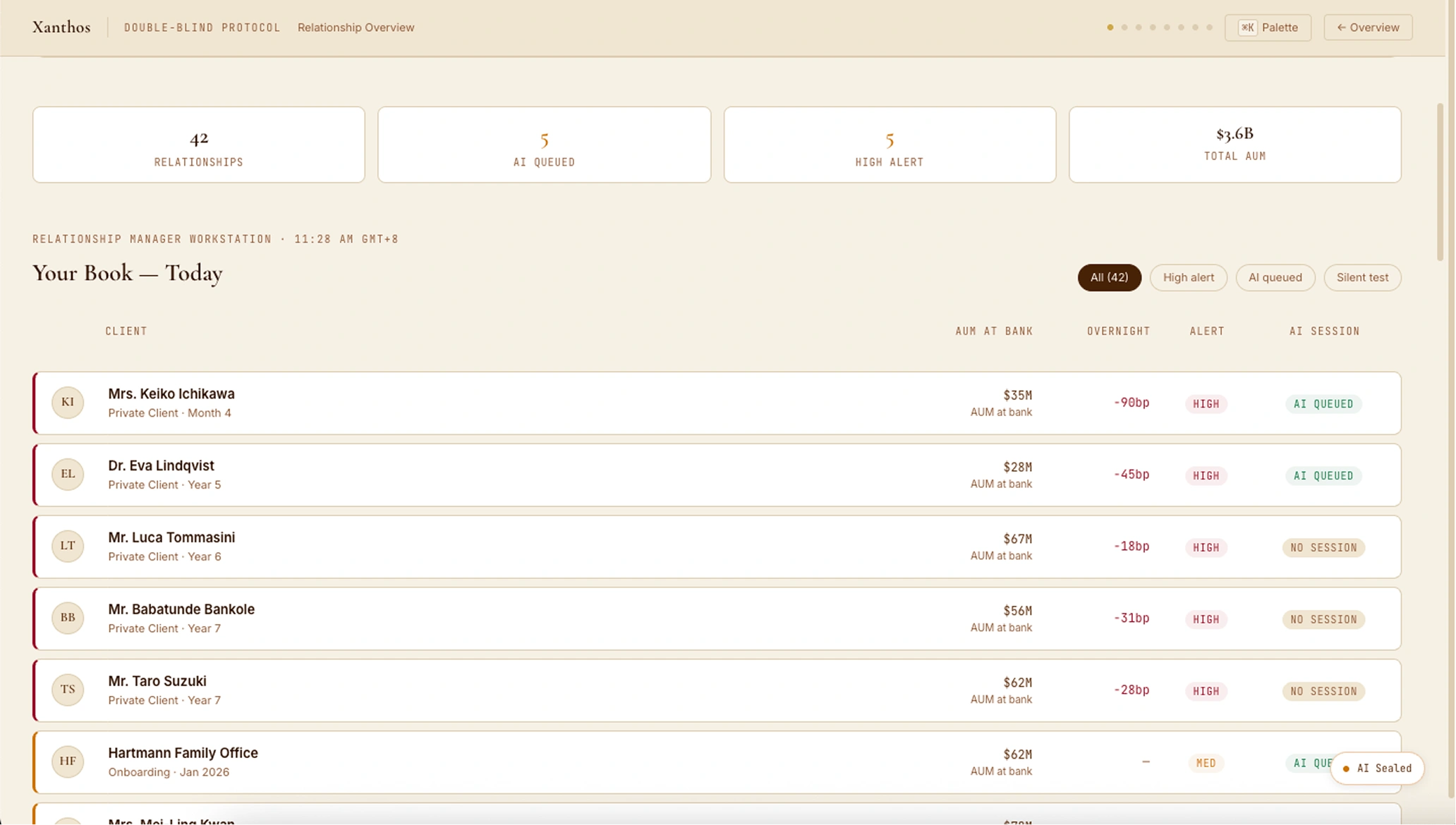
Screen 01 — Relationship Overview. Sorted by alert severity. AI queued counts visible; AI content sealed.
Alert Severity Sort
HIGH → MED → LOW → NONE. Within each tier, clients with queued AI sessions appear first. The RM sees the most urgent relationships at a glance without having to scan a flat list.
AI Sessions Sealed
"AI Queued" badge shows count only. The AI's analysis is completely invisible until the RM commits their own Track A read. This is the information wall's first enforcement layer — the RM cannot be anchored before they've committed.
Aggregate Intelligence
Stats strip shows computed aggregate AUM, session count, and alert breakdown. Five scenario chips in the hero banner let reviewers jump directly to any of the five scripted client scenarios.
Context before commitment.
Before the RM writes a single word, they see the full client context: overnight market events, portfolio snapshot, last conversation excerpt. The AI vault status sidebar confirms isolation is active. When the RM clicks "Begin Track A", a 700ms vault sealing animation plays — theatre that makes the protocol tangible.
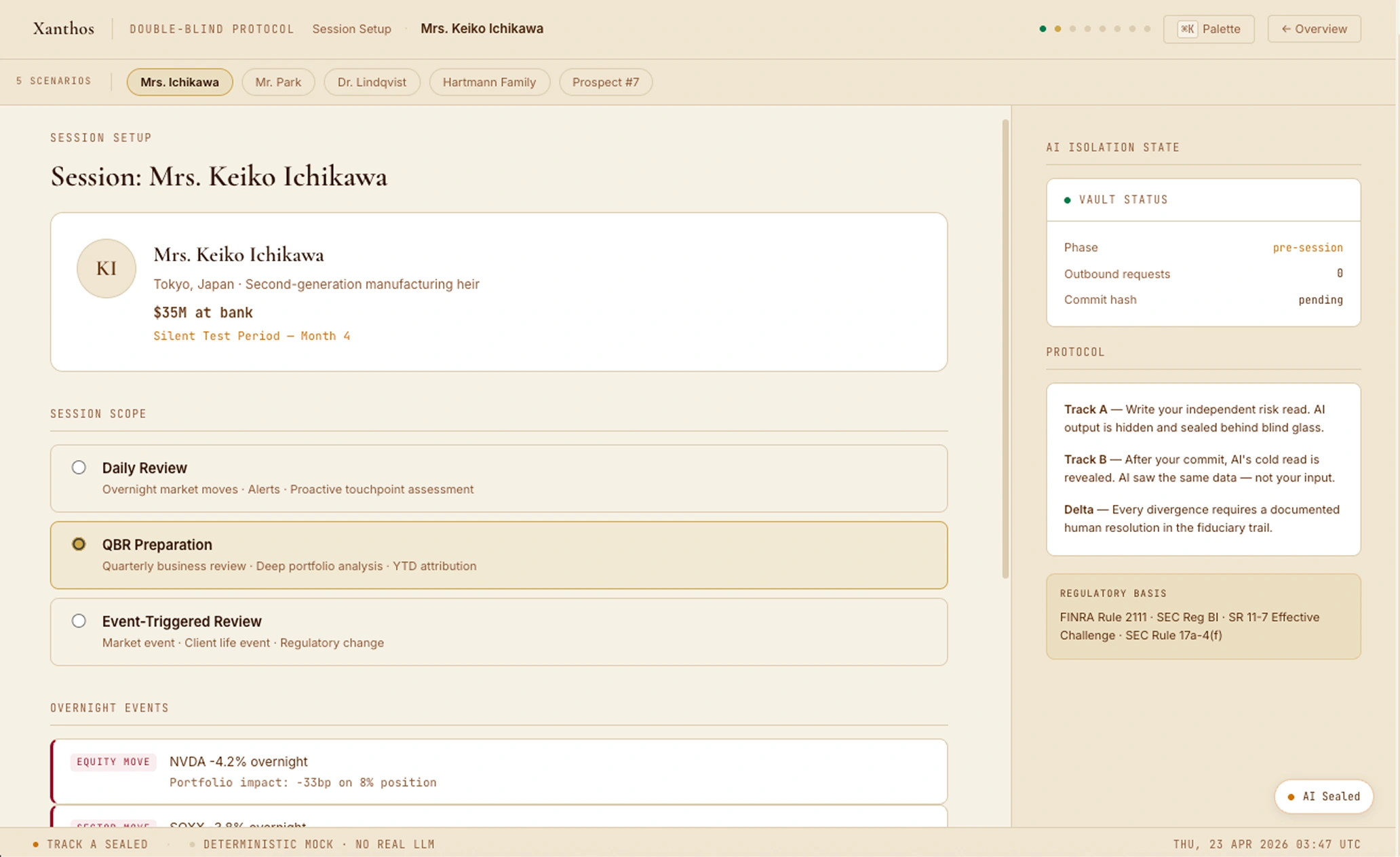
Screen 02 — Session Setup. Market events, FX context, client conversation. Vault sealed in sidebar.
Scenario-Specific Data Widgets
Each scenario surfaces relevant data prominently. For Ichikawa: a dedicated FX Psychology Risk widget showing USD/JPY overnight move and the JPY snapshot impact. For Lindqvist: a Turkey CDS spread bar chart. For Hartmann: an entity structure diagram flagging the BVI governance gap.
Last Conversation Context
"I'm worried tech is running too hot. If there's a correction I'd rather be positioned defensively. My late father always said the first loss is the best loss." — This is the client's mental model. The RM reads it before writing their own assessment.
Vault Status Sidebar
Phase: sealed. Outbound requests: 0. Commit hash: pending. The vault status sidebar is the first visible evidence of the protocol running. The RM knows exactly what the AI can and cannot see before they write anything.
Your read. AI sealed until you commit.
The RM writes their independent risk read in a split-view canvas. Left panel: raw client data. Right panel: input form. The amber pulsing "AI sealed" indicator at the top of the input panel makes the isolation tangible. Three required fields — risk read, recommended action, conviction level — gate the commit button.
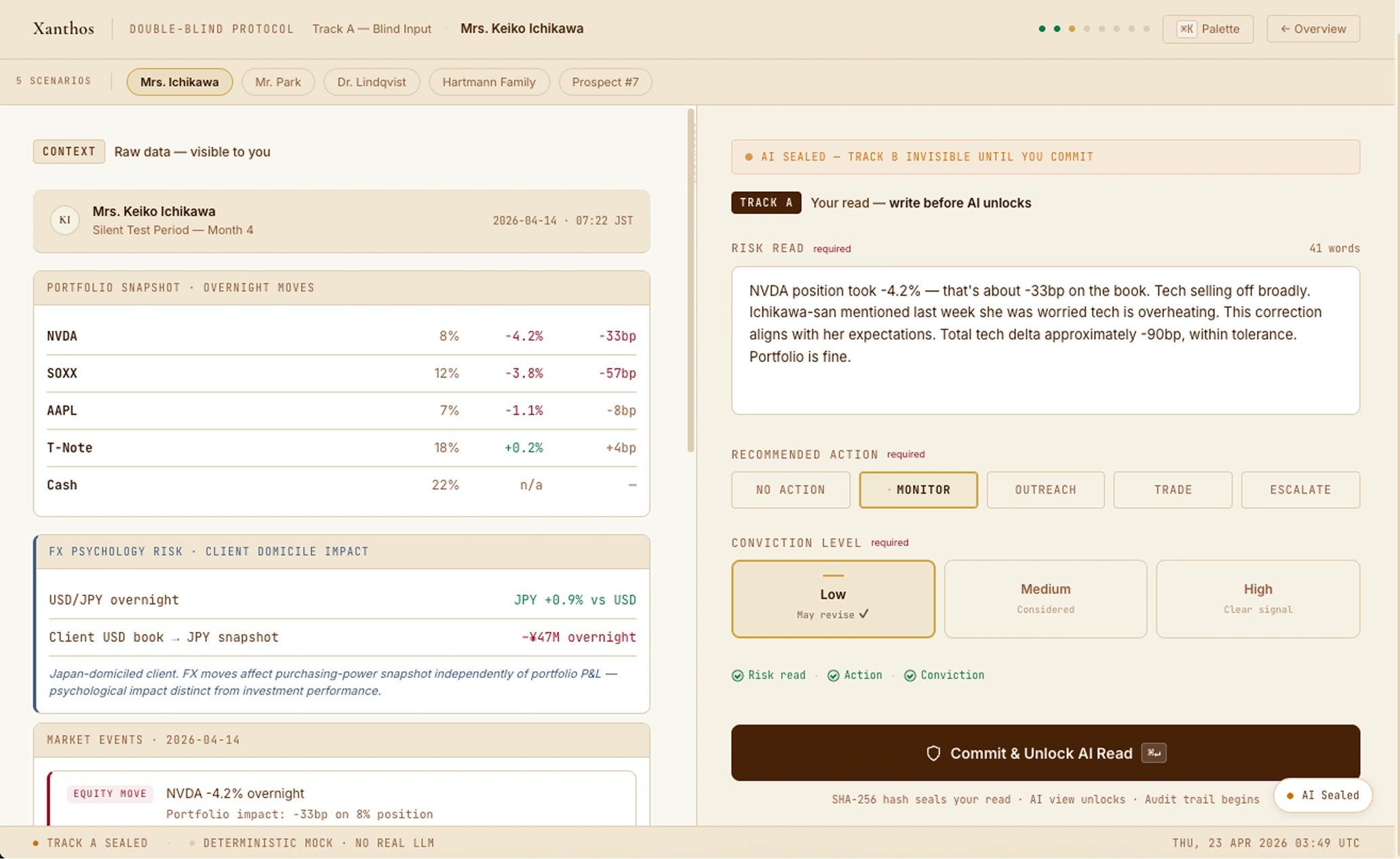
Screen 03 — Track A filled. MONITOR selected, LOW conviction, risk read complete. Commit sealed with SHA-256.
Auto-Resize Textarea
The risk read field grows with the RM's input. A live word count hint appears as they type. The placeholder text reinforces the protocol: "Write your independent view — AI is sealed until you commit."
Completeness Indicator
Three dots below the commit button track which required fields are filled: Risk Read · Action · Conviction. Each lights green when completed. The commit button remains disabled until all three are satisfied.
Keyboard Commit
⌘↵ commits the Track A input from anywhere in the form. The commit button shows the keyboard shortcut as a visible chip. For experienced RMs, the protocol should feel as fast as a well-practiced decision can be.
2.8 seconds. SHA-256 sealed. Network silent.
After commit, a terminal-style log plays. The hash is computed in real time via
crypto.subtle.digest('SHA-256') — the Web Crypto API, not a mock.
Nine timestamped log lines play sequentially. The hash reveal card shows the full
64-character hex string. Every claim here is verifiable in DevTools → Network:
0 outbound requests during Track A.
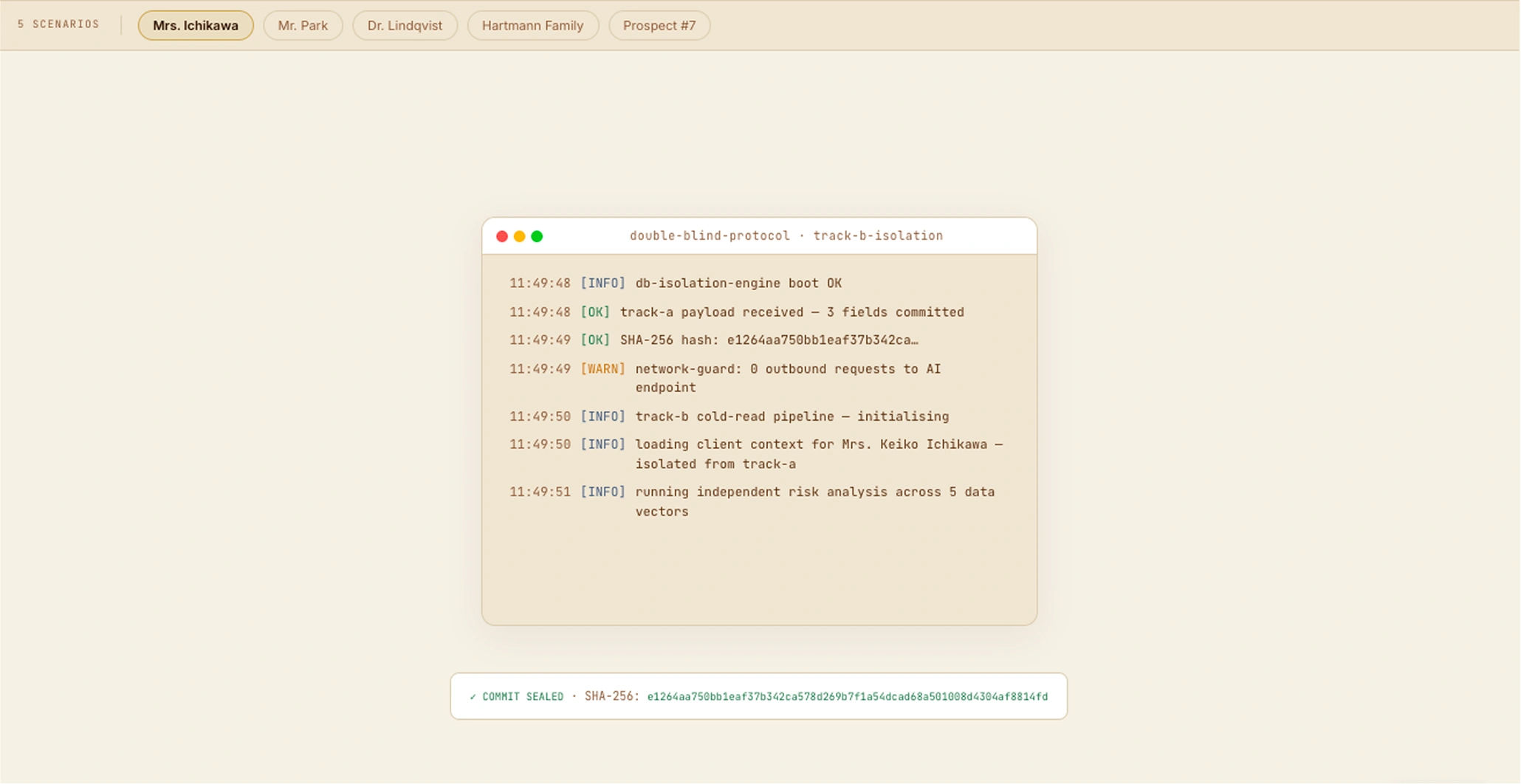
Screen 04 — Processing Terminal. Real SHA-256 hash. 9 timestamped log lines. Network guard: 0 outbound requests confirmed.
Design for collision, not consensus.
We don't auto-merge. We violently highlight divergence. Track A (RM) and Track B (AI) sit side by side, separated by a 2px copper rail. Delta ticks mark divergence points on the rail — each tick's color encodes the delta type. The AI's job isn't to smooth over human edges; the friction is the feature.
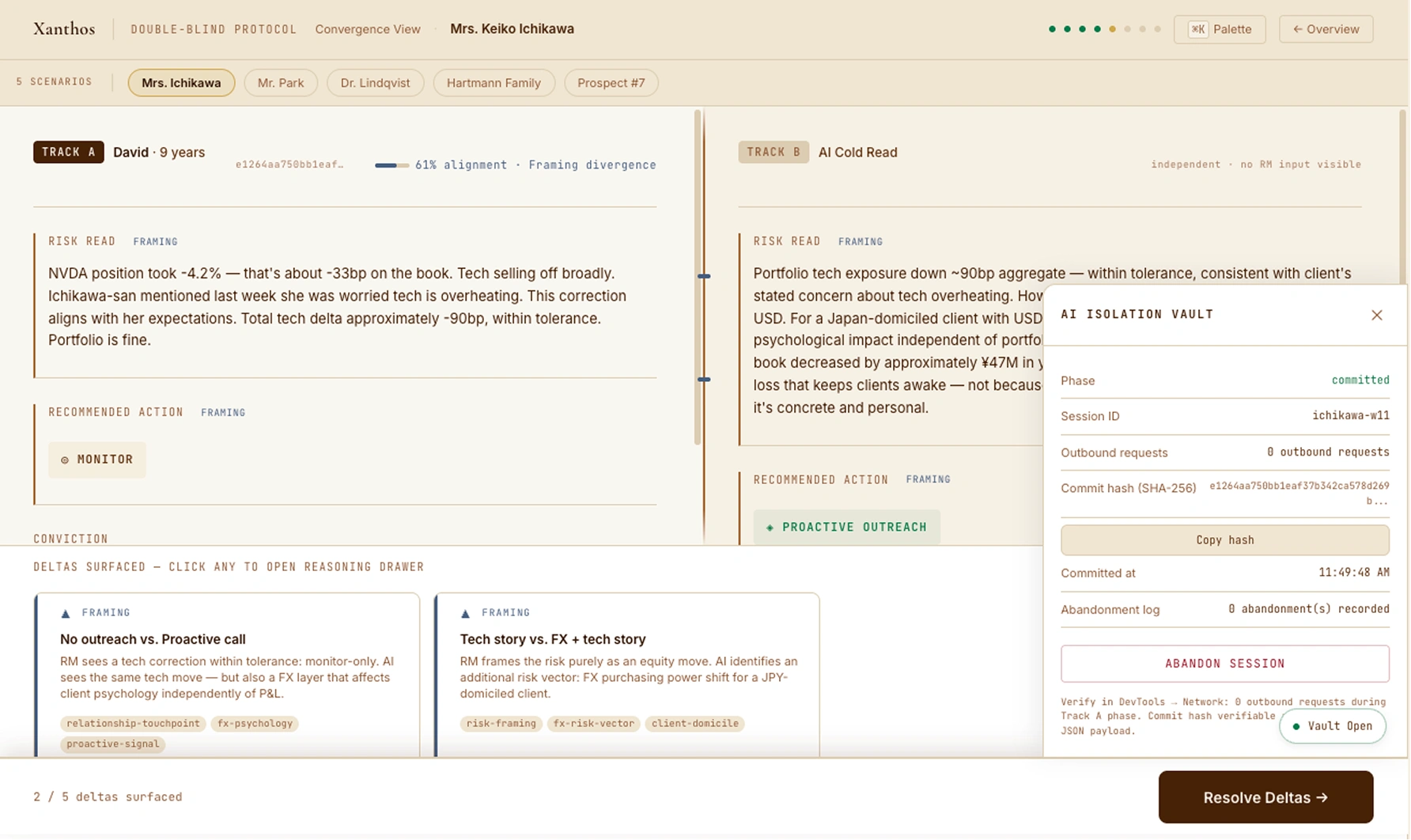
Screen 05 — Convergence View. Copper parallel rail divides two independent reads. 2 framing delta ticks. 61% alignment score.
Reasoning Drawer — Full Track A and Track B reads side by side. Delta position, AI rationale, regulatory auto-tags.
Delta Type Taxonomy
Five types with shape icons: ● Convergent (circle) · → Directional (arrow) · ▬ Magnitude (bar) · ◆ Framing (triangle) · — Null (dash). The framing delta is the Ichikawa scenario's delta: same action direction, different risk vector identified.
Field-Level Delta Markers
Each field row that has a corresponding delta shows a color-coded type badge inline in the label and a copper left border accent. The RM sees exactly which field the divergence is in — Risk Read, Recommended Action, or Conviction — without opening the drawer.
Reviewed State Tracking
Each delta card gets a green checkmark after the reasoning drawer is opened. The proceed bar shows "X of N deltas reviewed". When all are reviewed, the button turns green: "Ready to Resolve →". No forced progression — the RM can review at their own pace.
Every delta. One decision. Required reasoning.
The RM cannot proceed without resolving every surfaced delta. Four options — Hold / Adopt / Hybrid / Escalate — with required reasoning text for directional and magnitude deltas. Regulatory auto-tags appear automatically in the sidebar. A resolution summary strip updates in real time.
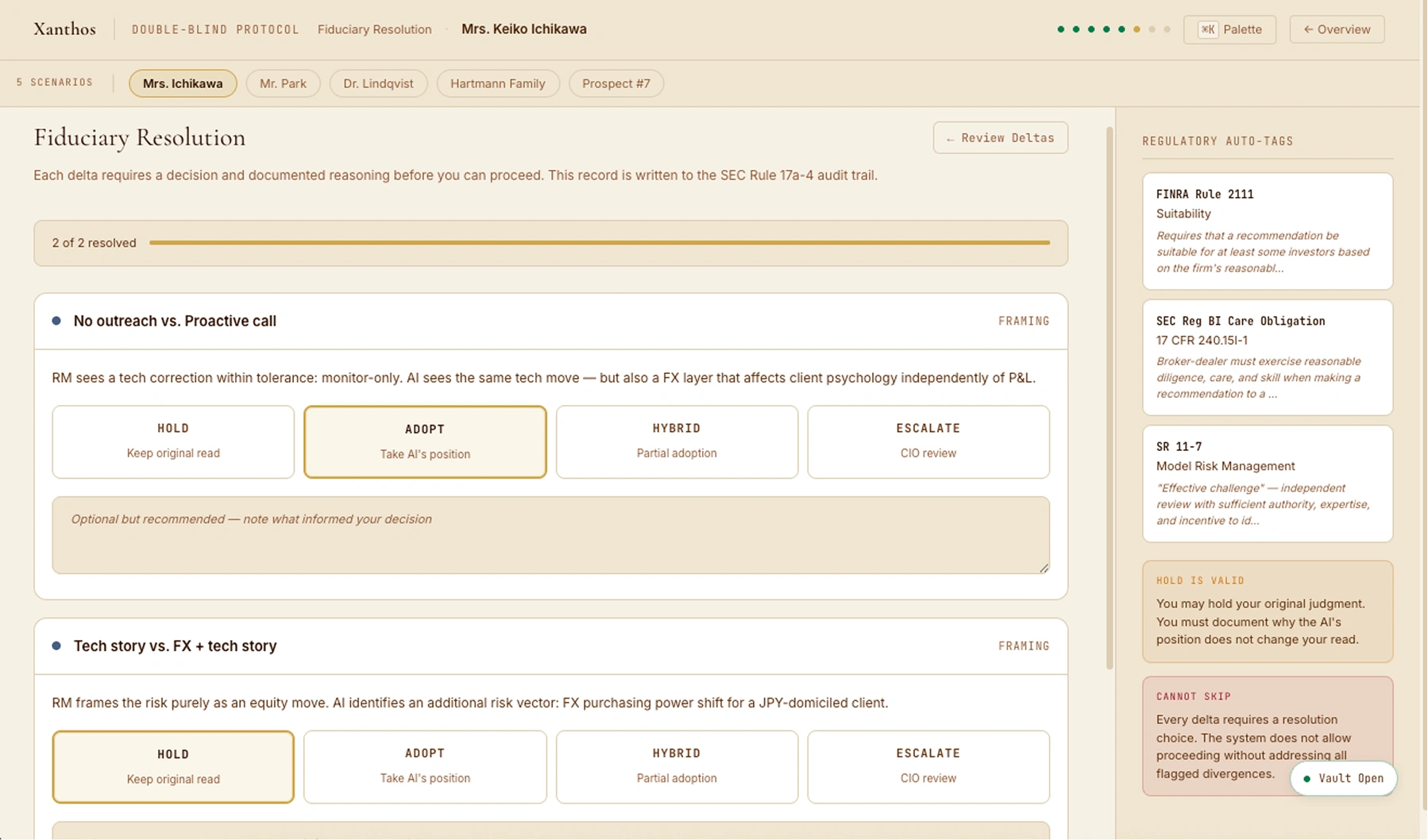
Screen 06 — Fiduciary Resolution. 2 of 2 resolved. HOLD on tech story delta, ADOPT on FX outreach delta. Regulatory auto-tags sidebar.
Progress Bar + Cannot Skip
A progress bar at the top tracks "X of N resolved." The proceed button stays disabled until every delta has a choice and required reasoning. For directional and magnitude deltas, the reasoning field is mandatory — the system enforces documentation of consequential decisions.
Regulatory Auto-Tags
FINRA Rule 2111, SEC Reg BI Care Obligation, and SR 11-7 are automatically tagged based on the delta type and resolution choice. The RM doesn't select them — the system annotates the reasoning with the applicable regulatory framework.
Back to Convergence
The RM can return to the Convergence View at any point during resolution to re-read either panel — without losing their reviewed delta state or partial resolution choices. No forced linear progression.
SEC Rule 17a-4. Immutable. Exportable.
The session produces a complete fiduciary audit record: session metadata, isolation verification with SHA-256 hash, Track A record, Track B record, delta summary, resolution reasoning, and regulatory attestation. Exportable as JSON with the commit hash embedded — any reviewer can verify the hash against the Track A payload.
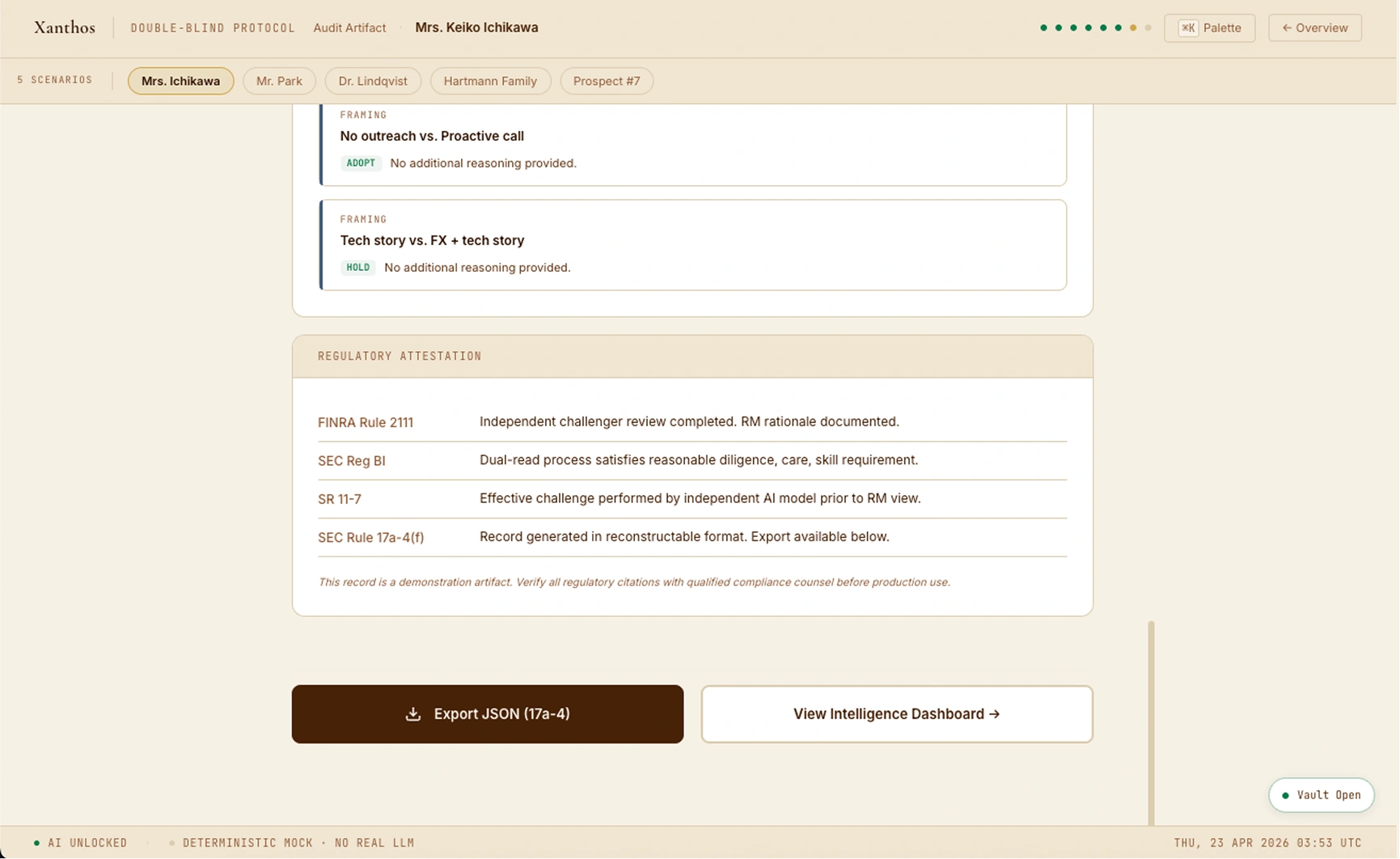
Screen 07 — Audit Artifact. Delta summary with resolutions. Regulatory attestation. Export JSON (17a-4 format).
Longitudinal value. Delta patterns. RM resolution bias.
After each session, the dashboard surfaces patterns: delta type distribution, RM resolution bias (adopt vs hold vs escalate), and historical session timeline. Over time, this view tells a story about both the relationship and the RM's judgment calibration. Open the live demo → to see the full Intelligence Dashboard after completing a session.
Silent Test Verdict
The intelligence dashboard surfaces the silent test period verdict and the ledger entry: "+1 — RM was proactive on FX angle before client had to ask." This is the metric that matters for UHNW relationship retention.
RM Resolution Bias
Supervisors can identify systemic patterns: RM always adopts AI = anchoring risk (AI dependency). RM always holds = potential dismissal without engagement. The bias bars show adopt / hold / hybrid / escalate proportions session over session.
Historical Session Timeline
Past sessions show date, scope (daily review / QBR prep), delta count, and outcome badge. For Ichikawa, three previous sessions demonstrate the relationship trajectory before Week 11 — including an earlier escalated magnitude delta that required CIO review.
Xanthos tokens. Three unique primitives.
Double-Blind inherits the Xanthos warm cream palette — the RM moving from the client portal to the workstation experiences the same institution at different depth. Three new visual primitives make the adversarial dual-read pattern tangible.
Convergence View — all three primitives visible: parallel rail (copper divider), delta ticks (framing type), and dissolved blind glass.
Six components. One verifiable record.
Every session produces a structured audit record with six distinct sections. Each is shown below. Together they satisfy SEC Rule 17a-4(f)'s reconstructable record requirement.
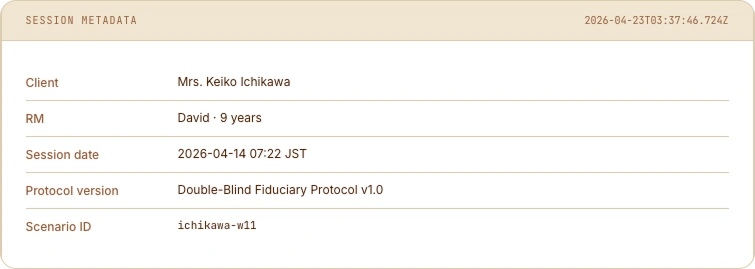
① Session Metadata — client, RM, date, scenario ID.

② AI Isolation Verification — SHA-256 hash + DevTools-verifiable 0 outbound requests.
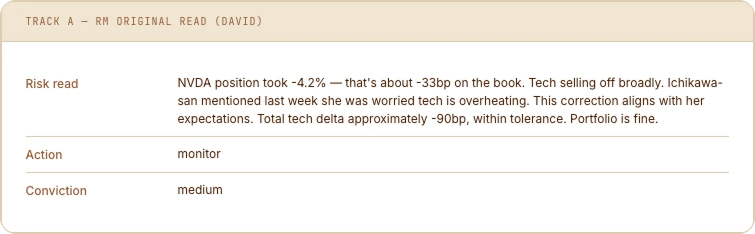
③ Track A — RM's committed read before AI view.
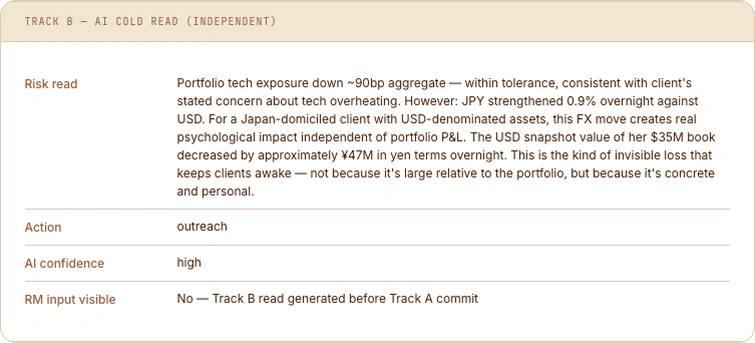
④ Track B — AI cold read. RM input: not visible.

⑤ Delta Summary — type, label, resolution choice.
⑥ Regulatory Attestation — FINRA 2111 · Reg BI · SR 11-7 · 17a-4.
⌘K to load any scenario. ? for shortcuts. / to search.
Command palette (⌘K) — fuzzy search across 5 scenarios, 3 navigate actions, demo trigger.
![Keyboard Shortcuts overlay on Convergence View — Navigation: ⌘K palette, / open, ? help, Esc dismiss, [ ] prev/next scenario. Session: ⌘↵ commit, Esc abandon, Watch hero demo replay.](img/Double_Blind/Double_Blind_keyboard.webp)
Keyboard shortcuts (?) — full navigation and session control. Convergence View behind.
Hartmann Family Office. Four jurisdictions. One governance gap.
The protocol adapts to each client context. For the Hartmann onboarding session, the AI Isolation Vault drawer is open — showing the sealed state before Track A begins. The Track B read will surface a BVI governance gap the RM's standard KYC review missed.
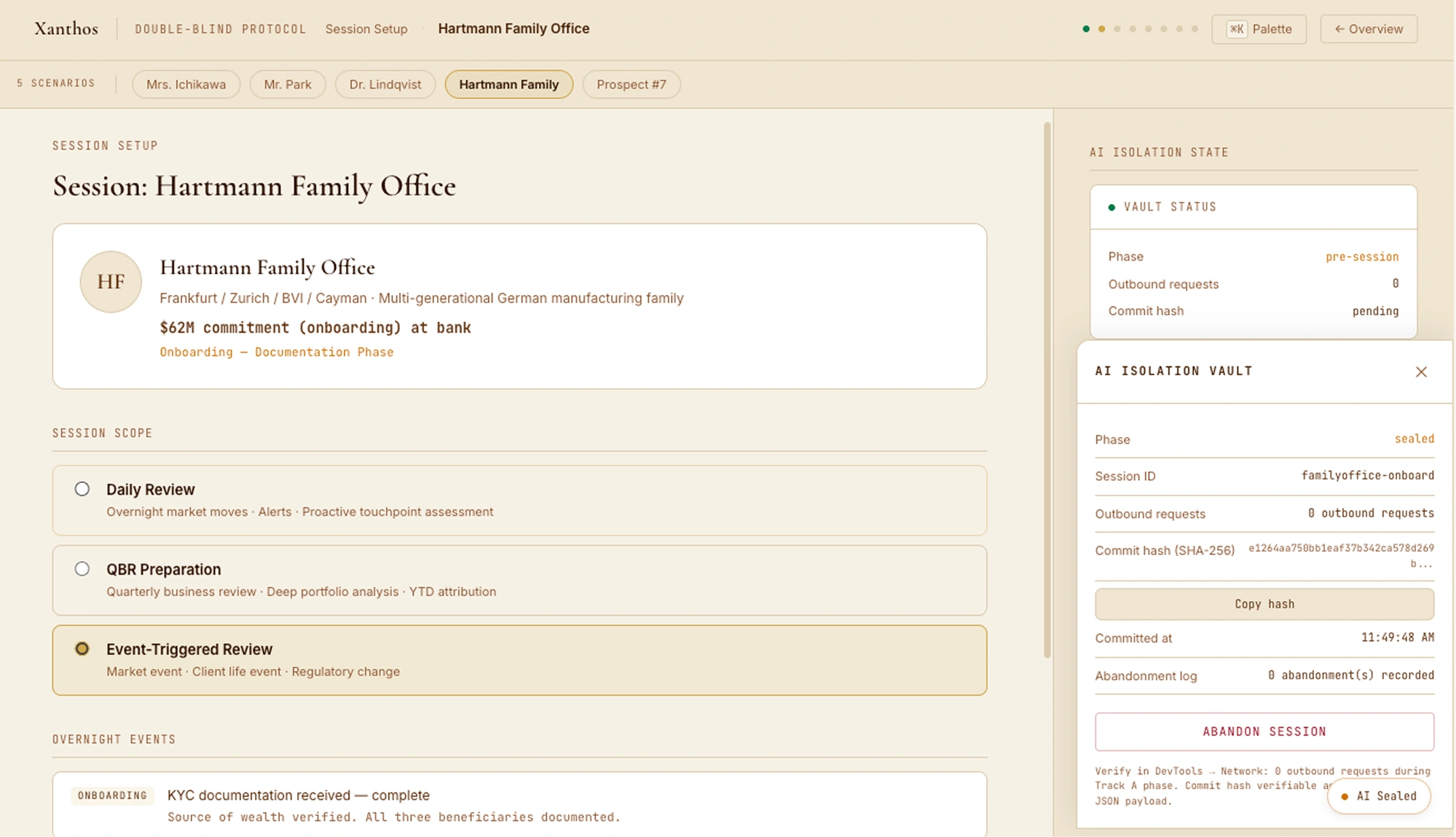
Hartmann Family Office — Session Setup with AI Isolation Vault drawer open. Sealed before Track A begins.
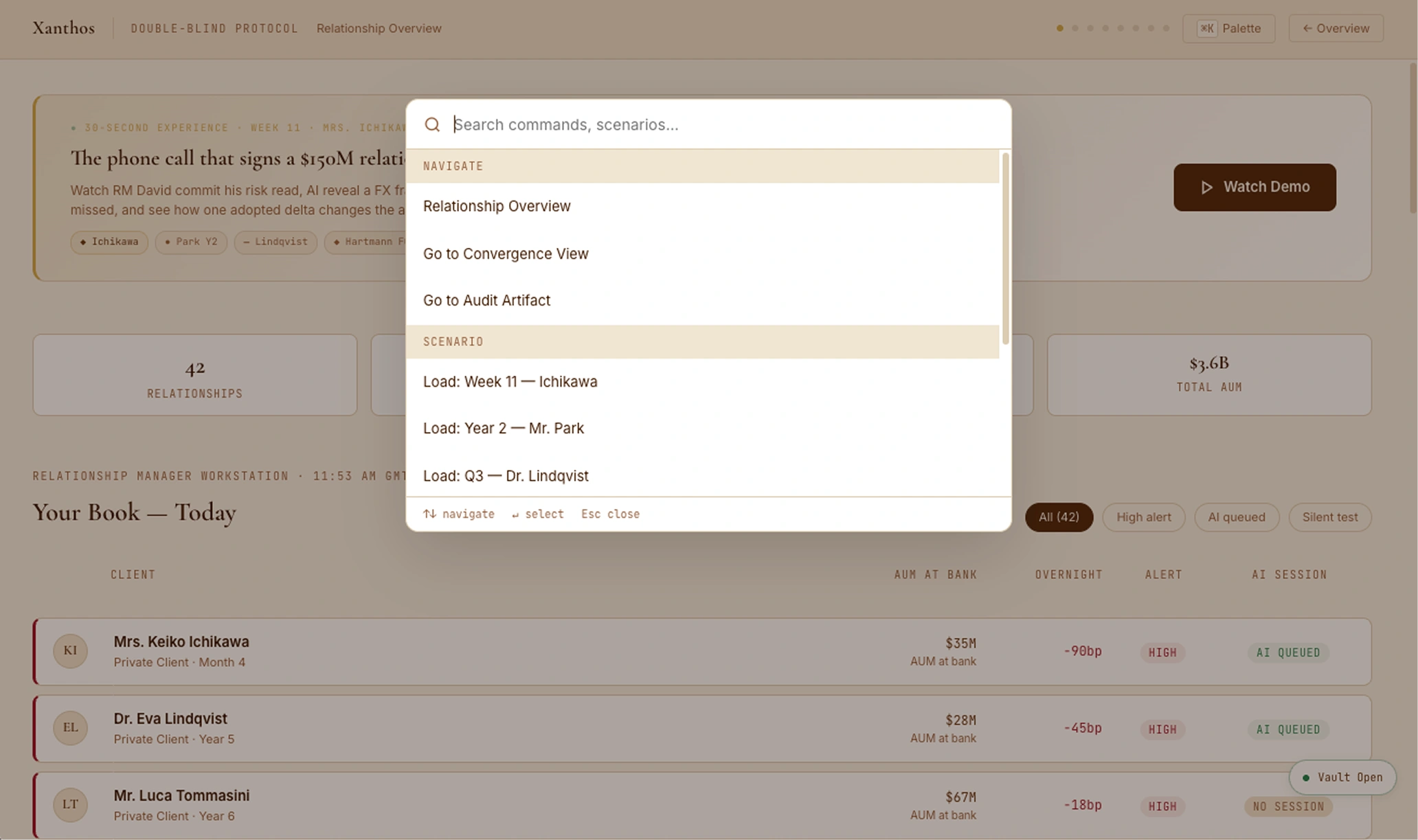
Each design decision has a regulation behind it.
Not retrofitted compliance. The regulatory structure generated the design decisions.
| Rule | Design implication | Where in the UI |
|---|---|---|
| FINRA Rule 2111 | Reasonable-basis suitability requires independent documented analysis. Track A + Track B dual read is the structural implementation. | Auto-tagged on Action and Conviction deltas in Resolution sidebar. |
| SEC Reg BI | Care Obligation: RM must exercise reasonable diligence, care, skill. The mandatory delta resolution with reasoning satisfies documentation of "reasonable." | Required reasoning field in Resolution. Auto-tagged on directional deltas. |
| SR 11-7 | "Effective challenge" — independent review with sufficient authority. RM-as-challenger is SR 11-7's effective challenge made into a UX pattern. | Vault drawer isolation confirmation. Convergent soft flag triggers CIO review prompt. |
| SEC 17a-4(f) | Electronic records: non-rewritable, timestamped, reconstructable. SHA-256 commit hash + timestamped audit trail is the compliance mechanism. | Audit Artifact screen (Screen 07). JSON export with hash chain. |
| EU AI Act Art. 14 | Human oversight of high-risk AI: the mandatory resolution step is Article 14's human-in-the-loop made structurally enforced. | RM cannot proceed without resolving every delta. Escalation always available. |
Regulatory references are design intent citations. Verify with qualified compliance counsel before production use.
Three projects. One complete picture.
Each piece stands alone. Together they form the full UHNW design arc: observed behaviour in the wild → the client portal → the RM trust layer.
For a Senior PD or Design Lead interview panel.
This concept evidences fiduciary-AI architecture thinking: the human RM commits first, SHA-256-sealed; AI reveals second; divergences require documented resolution before the client call. Regulatory anchors named by section: SEC Rule 17a-4(f) audit retention, SR 11-7 model-risk effective-challenge framework. Production foundations (4 years at ASIC-regulated ACY Securities + Xanthos sister concept) ground the relationship-manager workflow register; the double-blind protocol is the explicit concept extension.
What this concept deliberately does not claim. No AI is actually integrated; all outputs are deterministic pre-authored scenarios, not LLM inference. Not legal advice — 17a-4 and SR 11-7 citations are design-intent references, not regulatory opinions. No certified WCAG 2.1 AA conformance — full disclosure at the accessibility audit disclosure. No quantitative efficacy measurement on whether the double-blind protocol actually reduces AI-induced anchoring — the parallel methodology rigor for any future measurement would follow the Finlogix methodology disclosure (pre-registration, named limits, replication directions). No post-launch iteration data because there is no launch — the parallel pattern is at the ACY RG 268 iteration arc. The institutional adoption pattern for a fiduciary AI protocol inside a real private bank would follow the ACY Connect political-skill note register — the protocol’s commit/reveal interface IS its verification surface.
The disclosure register. The four 2026-05-18 field notes are the canonical voice this concept inherits from. Double-Blind sits at Scale 05 of the trust problem — the AI- governance form of the same discipline that runs through ACY (systemic), TradingCup (behavioural), ACY Connect (institutional), and Xanthos (relational).
- Finlogix Cohen’s d = 2.47 disclosure
- n = 15 paired within-subjects design
- Seven limits named
- Eight-direction replication plan
- RG 268 disclosure surface, 18 months
- v1 modal → v2 strip → v3 inline
- Muscle-memory dismissal failure named
- Honest negative result on AUM lift
- 12 token contrast pairs measured
- ARIA + keyboard patterns documented
- Six limits named
- Six-component replication plan with cost estimates
- ACY Connect, 12 institutional clients
- One IT director who didn’t want to migrate
- Three credible objections named
- Three verification surfaces that earned adoption
Where this sits in the body of work
Follow these threads across the portfolio to see the same problem solved differently.